3.5. Viewing Alerts and Audit Log and Sending E-mail Notifications¶
This section describes Acronis Cyber Infrastructure alerts and audit log and how to send out e-mail notifications about alerts, warnings, and errors.
3.5.1. Viewing Alerts¶
The Alerts tab lists all the alerts logged by Acronis Cyber Infrastructure. An alert is generated and logged each time one of the following conditions is met or events happen:
- a critical issue has happened with a cluster, its components (CS, MDS), disks, nodes, or services;
- cluster requires configuration or more resources to build or restore its health;
- network requires configuration or is experiencing issues that may affect performance;
- license is about to expire or has expired;
- cluster is about to or has run out of available space.
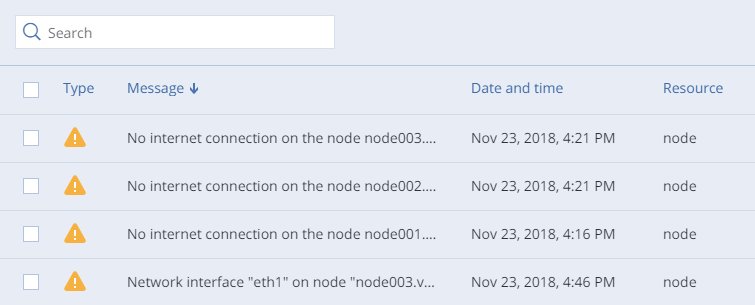
To view the details of an alert, select it on the MONITORING > Alerts screen and click Details in the menu on the right.
Alerts can be ignored (deleted from the alerts list) or postponed for several hours. Postponed alerts reappear in the list after some time.
To ignore or postpone an alert, select it and click the corresponding button.
3.5.2. Viewing Audit Log¶
The MONITORING > Audit log screen lists all management operations performed by users and their activity events.
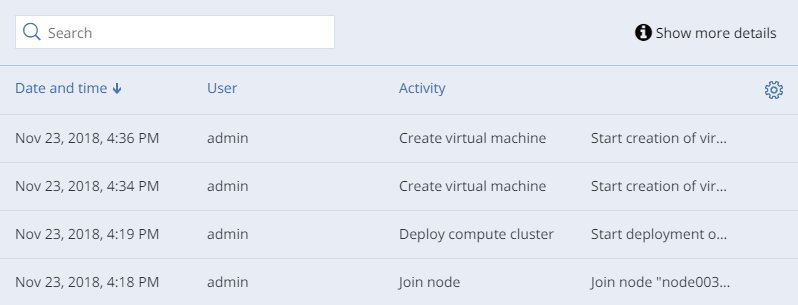
To view detailed information on a log entry, select it and click Show more details.
3.5.3. Sending E-mail Notifications¶
Acronis Cyber Infrastructure can send automatic e-mail notifications about errors, warnings, and alerts.
To set up e-mail notifications, do the following:
On the SETTINGS > Advanced settings > NOTIFICATIONS tab, specify the following information:
In the From and Sender name fields, the notification sender’s e-mail and name.
In the To field, one or more notification recipient e-mails, one per line.
In the User account and User password fields, the credentials of the notification sender registered on the SMTP server.
In the SMTP server field, the DNS name of the SMTP server, either public (e.g.,
smtp.gmail.com) or the one in your organization.The management node must be able to access the SMTP server.
If required, a custom SMTP port the server uses.
In the Security field, the security protocol of the SMTP server.
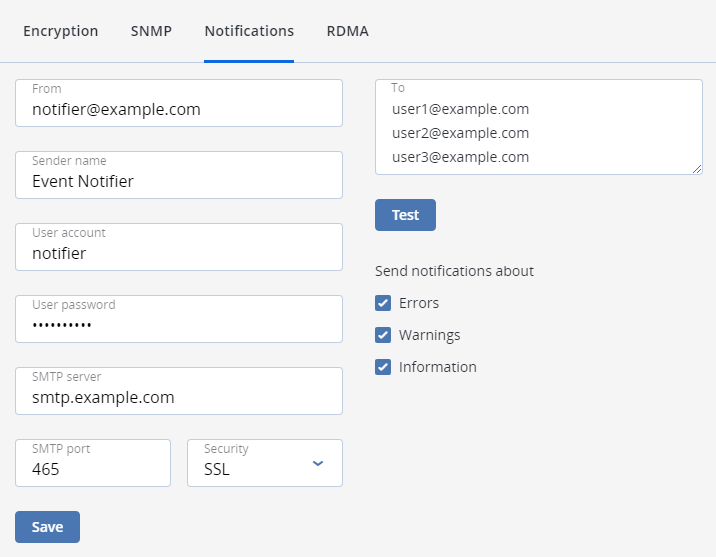
Tick the checkboxes for alerts you want to be notified about.
Click Save.
To send a test e-mail, specify your e-mail registered on the SMTP server in both the From and To fields and click Test.
