2.1. Managing Networks and Traffic Types¶
To balance and optimize networking in Acronis Cyber Infrastructure, you can assign different types of traffic to separate networks. Assigning a traffic type to a network means that a firewall is configured on nodes connected to this network, specific ports are opened on node network interfaces, and the necessary iptables rules are set. For example, nodes connected to a network with only the S3 public traffic type will accept incoming connections only on ports 80 and 443.
As described in the Installation Guide, is it recommended to have these networks in Acronis Cyber Infrastructure:
For internal storage traffic (traffic types: Storage, Internal management, OSTOR private, ABGW private), assigned to the first bonded connection;
Note
If you plan to use RDMA over InfiniBand, move the traffic type Storage to a dedicated network and assign that network to the IB interface. See Enabling RDMA.
For overlay networking (traffic type VM private), assigned to a VLAN created on the second bonded connection;
For management and API (traffic types: Admin panel, SSH, SNMP, Compute API, Self-service panel), assigned to a VLAN created on the second bonded connection;
For external networking (traffic types: VM public, S3 public, ABGW public, iSCSI, and NFS), assigned to a VLAN created on the second bonded connection.
You need to configure these networks on the INFRASTRUCTURE > Networks screen on the admin panel before you create the cluster (see Creating, Editing, and Deleting Networks). By default, you have two preconfigured networks: Public and Private. They can be considered as templates that you can customize to create the desired (recommended) configuration.
Note
Some traffic types cannot be reassigned to a different network if they are in use.
After you create the networks, proceed to create the remaining of the recommended VLAN interfaces on each node and assign them to networks as described in Creating VLAN Interfaces.
An example of recommended networks and their traffic types is:
| Network | Traffic types |
|---|---|
| Public | Compute API, Admin panel, SSH, SNMP, Self-service panel |
| Private | Storage, Internal management, OSTOR private, ABGW private |
| Overlay | VM private |
| Export | S3 public, iSCSI, NFS, ABGW public, VM public |
The next three subsections describe all traffic types that can be assigned to networks.
2.1.1. Exclusive Traffic Types¶
Exclusivity means that such a traffic type can be added only to one network. Exclusive traffic types cannot be reassigned between networks if they are in use. To do that, you will have to delete the service that uses them first.
- Internal management
- Internal cluster management and transfers of node monitoring data to the admin panel. Without this traffic type, the administrator cannot control and monitor the cluster. The cluster, however, continues working.
- Storage
- Internal transfers of data chunks, high availability service heartbeats, as well as data self-healing. This is the most critical traffic type that defines storage performance and enables cluster HA.
- OSTOR private
- Internal data exchange between multiple S3/NFS services.
- ABGW private
- Internal management of and data exchange between multiple ABGW services.
- VM private
- Network traffic between VMs in private virtual networks and VNC console traffic. Private virtual networks are implemented as VXLAN, overlay networking fully isolated on L2.
- Compute API
- External access to standard OpenStack API endpoints. Opens TCP ports 5000, 6080, 8004, 8041, 8774, 8776, 8780, 9191, 9292, 9696.
2.1.2. Regular Traffic Types¶
The traffic types listed further are not exclusive and can be added to multiple networks.
- S3 public
- External data exchange with the S3 access point. Uses TCP ports 80 and 443.
- iSCSI
- External data exchange with the iSCSI access point. Uses TCP port 3260.
- NFS
- External data exchange with the NFS access point. Uses TCP/UDP ports 111, 892, and 2049.
- ABGW public
- External data exchange with Acronis Backup agents and Acronis Backup Cloud. Uses TCP port 44445.
- Admin panel
- External access to the admin panel. Uses TCP port 8888.
- VM public
- External data exchange between VMs and public networks (e.g., the Internet). When a node network interface is assigned to a network with this traffic type, an Open vSwitch bridge is created on that network interface.
- SSH
- Remote access to nodes via SSH. Uses TCP port 22.
- SNMP
- External access to storage cluster monitoring statistics via the SNMP protocol. Opens UDP port 161.
- Self-service panel
- External access to the self-service panel. Opens TCP port 8800.
2.1.3. Custom Traffic Types¶
You can create custom traffic types that will open desired TCP ports. Such traffic types can be added to multiple networks. See Creating, Editing, and Deleting Traffic Types.
2.1.4. Creating, Editing, and Deleting Networks¶
If required, you can add a new network by doing as follows:
On the INFRASTRUCTURE > Networks screen, click Edit and then Create network.
In the New network window, specify a network name. Network names must be alphanumerical and 2-32 characters long.
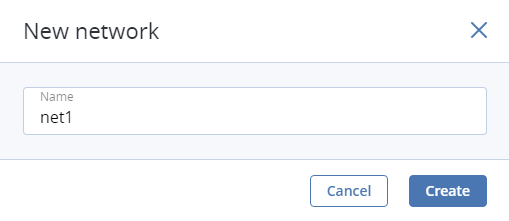
Click Create.
Add the needed traffic types to the new network by ticking the corresponding checkboxes.
When finished, click Save to apply the changes.
To edit a network name or delete a custom network, click on the ellipsis icon next to it and select the action you want to perform.
You can only delete networks that are not assigned to any network adapters.
2.1.5. Creating, Editing, and Deleting Traffic Types¶
If required, you can add a new traffic type by doing as follows:
On the INFRASTRUCTURE > Networks screen, click Edit and then Create traffic type.
In the Create traffic type window, specify a traffic type name and port to open.
Traffic type names must be alphanumerical and 3-32 characters long.
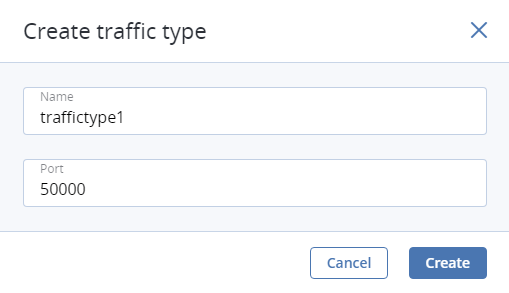
Click Create.
Add the newly created traffic type to one or more of your networks by ticking the corresponding checkboxes.
When finished, click Save to apply the changes.
To edit or delete a custom traffic type, make sure it is excluded from all networks, click the ellipsis icon next to it, and select the desired action.
